网上二手书网站开发中的问题和展望自助网站免费建站平台
问题描述:
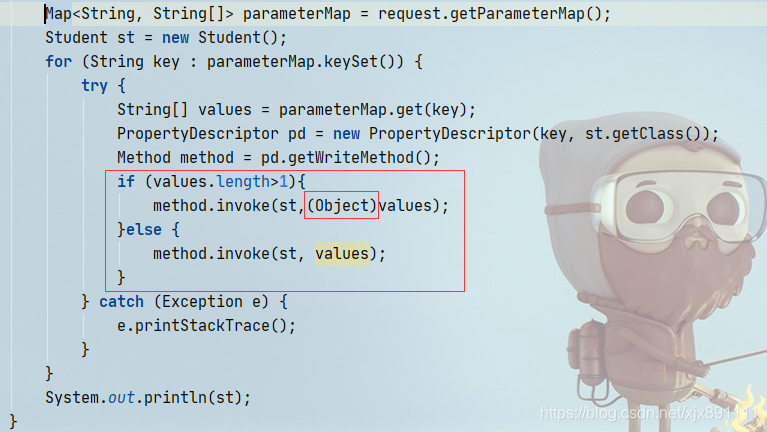
在使用method.invoke()方法时,遇到了一个问题,就是,在传递第二个参数时,如果传递的是数组,如果数组中只有一个数据时,不需要强转,也不能强转,而如果数组中数据长度大于1时,需要强转成object. 否则报错(IllegalArgumentException).
如下图:
首先,明确一下method.invoke()方法的具体声明:
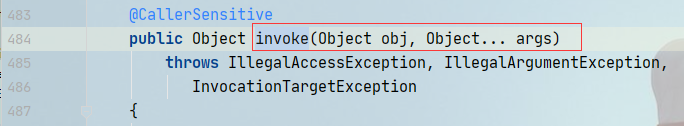
invoke方法里有两个参数,第一个是object类型,这个是传具体的类对象的.第二个参数args,是可变参数,其实底层就是一个数组.
问题也出在第二个参数上,为什么底层是数组,而我直接给传数组,还要看长度,长度大于1时需要强转呢.
其实答案很简单,问题出在相关javaBean(student)类中.类中定义如下:
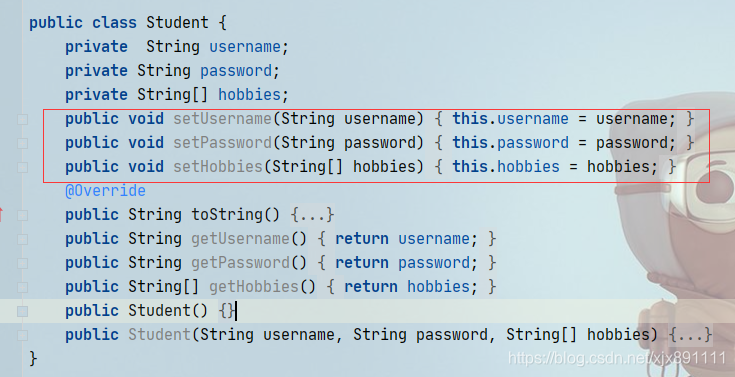
类中定义了三个参数.其中,username 和password 中的set方法的入参都是String,而hobbies中set方法入参是String数组.
以setUsername为例, 这里再来解释一下method.invoke()方法.
这里method:具体指setUsername.
method.invoke()方法中,第一个参数是student类中的实例.
第二个参数就是对应方法中的形参.如果有几个形参,这里就需要传几个参数即可.如果没有可以不传.
这里setUsername中有一个形参,所以可以传一个String参数.
或者传一个含一个参数的数组也可以,因为invoke方法中第二个参数是可变参,也就是数组,如果传的是参数,invoke方法也会自动转为数组的.
这里再来看setHobbies, 这里setHobbies中也是有一个形参,所以可以传一个数组参数,但是问题来了,这时,java怎么知道你传的是一个参数.还是具有多个形参的参数.这时,java都是会将这个当成可变参来处理的, 所以这个时候就会报错了,它以为你传的是有多个参数的setHobbies方法,但是你的setHobbies方法只有一个数组形参.所以就报错了.(参数个数不正确,这也印证了java会将他当可变参处理)
这时就需要处理一下,让java能识别我是一个参数,而不是多个参数,怎么办?
两种解决方案:
1. 定义一个二维数组,将实参传递到这个二维数组[0]中,这时java在调用invoke方法时,就会自动解析成一个参数.2. 强转成一个整体.这时就可以利用(Object)强转,这时这个数组就是一个整体了,java这时就不会将这个数组处理成可变参了.而是将他就当成一个数组参数来处理.
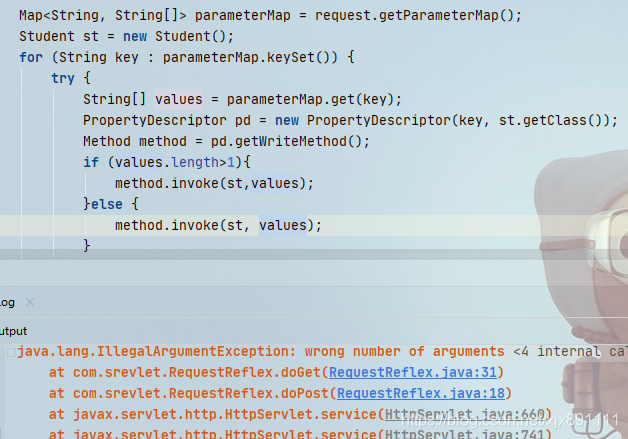
这也解决了另一个问题,就是如果我都强转,怎么也不行?
**如果都强转的话,类型就都变成数组类型了哦,这时虽然也都是一个参数,但是如果形参不是数组的,就会报参数类型不匹配.**如setUsername.
